| app | ||
| fastlane/metadata/android | ||
| gradle/wrapper | ||
| libpdfviewer@2296593275 | ||
| .gitignore | ||
| .gitmodules | ||
| build.gradle | ||
| BUILD.md | ||
| DONATE.txt | ||
| gradle.properties | ||
| gradlew | ||
| gradlew.bat | ||
| LICENSE.txt | ||
| README.md | ||
| settings.gradle | ||
| TODO.md | ||
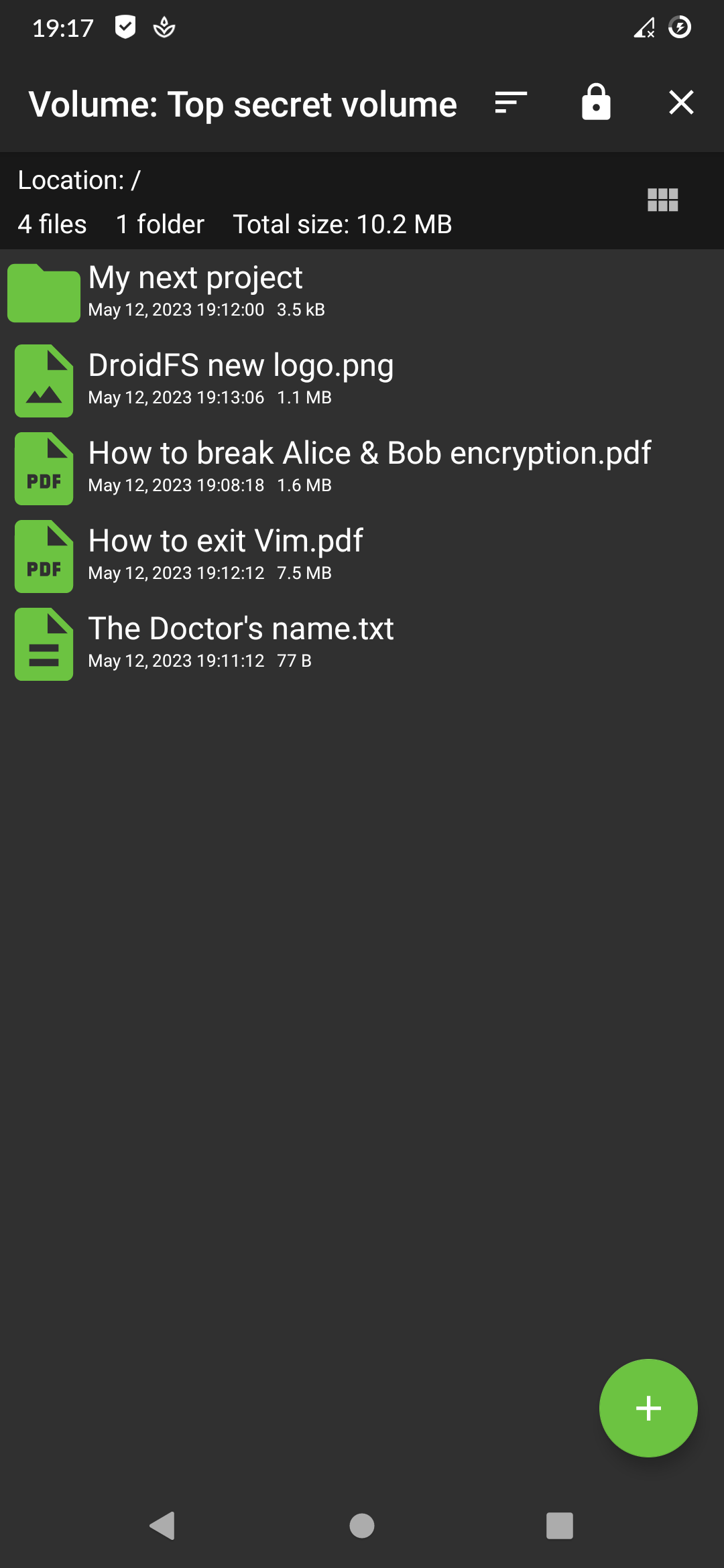
DroidFS
An alternative way to use encrypted virtual filesystems on Android that uses its own internal file explorer instead of mounting volumes. It currently supports gocryptfs and CryFS.
For mortals: Encrypted storage compatible with already existing softwares.

Support
The creator of DroidFS works as a freelance developer and privacy consultant. I am currently looking for new clients! If you are interested, take a look at the website. Alternatively, you can directly support DroidFS by making a donation.
Thank you so much ❤️.
Disclaimer
DroidFS is provided "as is", without any warranty of any kind. It shouldn't be considered as an absolute safe way to store files. DroidFS cannot protect you from screen recording apps, keyloggers, apk backdooring, compromised root accesses, memory dumps etc. Do not use this app with volumes containing sensitive data unless you know exactly what you are doing.
Features
- Compatible with original encrypted volume implementations
- Internal support for video, audio, images, text and PDF files
- Built-in camera to take on-the-fly encrypted photos and videos
- Unlocking volumes using fingerprint authentication
- Volume auto-locking when the app goes in background
For upcoming features, see TODO.md.
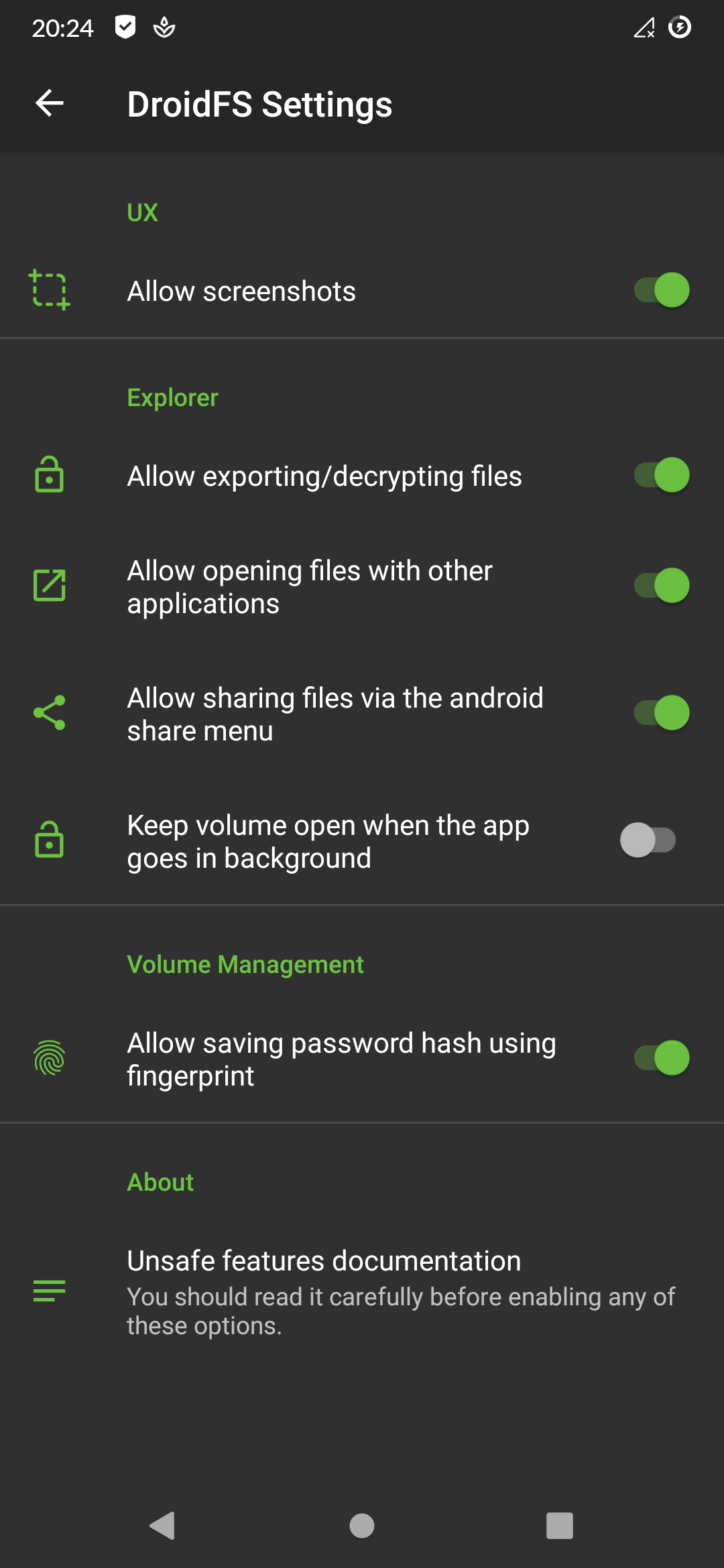
Unsafe features
Some available features are considered risky and are therefore disabled by default. It is strongly recommended that you read the following documentation if you wish to activate one of these options.
Allow screenshots:
Disable the secure flag of DroidFS activities. This will allow you to take screenshots from the app, but will also allow other apps to record the screen while using DroidFS.Note: apps with root access don't care about this flag: they can take screenshots or record the screen of any app without any permissions.
Allow exporting files:
Decrypt and write file to disk (external storage). Any app with storage permissions could access exported files.Allow sharing files via the android share menu*:
Decrypt and share file with other apps. These apps could save and send the files thus shared.Allow saving password hash using fingerprint:
Generate an AES-256 GCM key in the Android Keystore (protected by fingerprint authentication), then use it to encrypt the volume password hash and store it to the DroidFS internal storage. This require Android v6.0+. If your device is not encrypted, extracting the encryption key with physical access may be possible.Keep volume open when the app goes in background:
Don't close the volume when you leave the app but keep running it in the background. Anyone going back to the activity could have access to the volume.Allow opening files with other applications*:
Decrypt and open file using external apps. These apps could save and send the files thus opened.Expose open volumes*:
Allow open volumes to be browsed in the system file explorer (DocumentProvider API). Encrypted files can then be selected from other applications, potentially with permanent access. This feature requires "Keep volume open when the app goes in background" to be enabled.Grant write access:
Files opened with another applications can be modified by them. This applies to both previous unsafe features.
* These features may require temporarily writing the plain file to disk (DroidFS internal storage). This file can be read by applications with root access or by physical access if your device is not encrypted. For files small enough and on a 3.17+ kernel, DroidFS will try to use memory-only storage using memfd_create(2) (can break some apps).
Download

You can download DroidFS from F-Droid or from the "Releases" section in this repository.
APKs available here are signed with my PGP key available on keyservers:
gpg --keyserver hkps://keyserver.ubuntu.com --recv-keys AFE384344A45E13A
Fingerprint: B64E FE86 CEE1 D054 F082 1711 AFE3 8434 4A45 E13A
Email: Hardcore Sushi <hardcore.sushi@disroot.org>
To verify APKs, save the PGP-signed message to a file and run gpg --verify <the file>. Don't install any APK if the verification fails !
If the signature is valid, you can compare the SHA256 checksums with:
sha256sum <APK file>
Don't install the APK if the checksums don't match!
F-Droid APKs should be signed with the F-Droid key. More details here.
Permissions
DroidFS needs some permissions for certain features. However, you are free to deny them if you do not wish to use these features.
Read & write access to shared storage:
Required to access volumes located on shared storage.Biometric/Fingerprint hardware:
Required to encrypt/decrypt password hashes using a fingerprint protected key.Camera:
Required to take encrypted photos or videos directly from the app.Record audio:
Required if you want sound on video recorded with DroidFS.
Limitations
DroidFS works as a wrapper around modified versions of the original encrypted container implementations (libgocryptfs and libcryfs). These programs were designed to run on standard x86 Linux systems: they access the underlying file system with file paths and syscalls. However, on Android, you can't access files from other applications using file paths. Instead, one has to use the ContentProvider API. Obviously, neither Gocryptfs nor CryFS support this API. As a result, DroidFS cannot open volumes provided by other applications (such as cloud storage clients). If you want to synchronize your volumes on a cloud, the cloud application must synchronize the encrypted directory from disk.
Due to Android's storage restrictions, encrypted volumes located on SD cards must be placed under /Android/data/sushi.hardcore.droidfs/ if you want DroidFS to be able to modify them.
Building from source
You can follow the instructions in BUILD.md to build DroidFS from source.
Third party code
Thanks to these open source projects that DroidFS uses:
Modified code:
- Encrypted filesystems (to protect your data):
- libgocryptfs (forked from gocryptfs)
- libcryfs (forked from CryFS)
- libpdfviewer (forked from PdfViewer) to open PDF files
- DoubleTapPlayerView to add double-click controls to the video player
Borrowed code:
- MaterialFiles for Kotlin natural sorting implementation